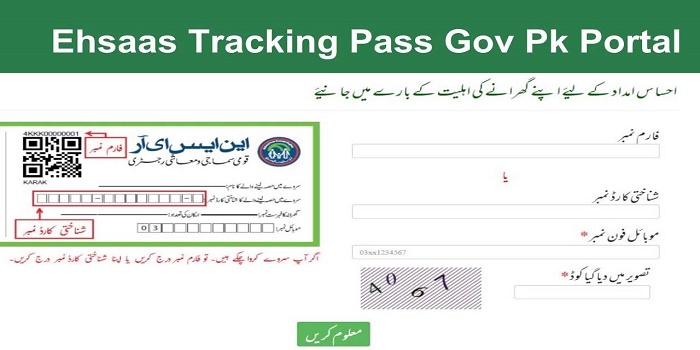
At Ehsaas Program, open from https://ahsasprogram.com/, one of our fundamental needs is the protection of our guests. This Protection Strategy archive contains kinds of data that is gathered and recorded by Ehsaas Program and how we use it. Assuming you have extra inquiries or require more data about our Protection Strategy, go ahead and us. This Security Strategy applies just to our web-based exercises and is substantial for guests to our site concerning the data that they shared as well as gather in Ehsaas Program. This approach isn’t pertinent to any data gathered disconnected or through channels other than this site.
Data we gather
The individual data that you are approached to give, and the justifications for why you are approached to give it, will be clarified to you at the point we request that you give your own data. In the event that you reach us straightforwardly, we might get extra data about you, for example, your name, email address, telephone number, the items in the message or potentially connections you might send us, and some other data you might decide to give. At the point when you register for a Record, we might request your contact data, including things, for example, name, organization name, address, email address, and phone number.
How we utilize your data
We utilize the data we gather in different ways, including to:
- Give, work, and keep up with our site
- Improve, customize, and extend our site
- Comprehend and dissect how you utilize our site
- Foster new items, administrations, elements, and usefulness
- Speak with you, either straightforwardly or through one of our accomplices, including for client assistance, to furnish you with refreshes and other data connecting with the site, and for showcasing and special purposes
- Send you messages
- Find and forestall misrepresentation
Log Documents
Ehsaas Program observes a guideline system of utilizing log documents. These records log guests when they visit sites. All facilitating organizations do this and a piece of facilitating administrations’ investigation. The data gathered by log documents incorporate web convention (IP) addresses, program type, Network access Supplier (ISP), date and time stamp, alluding/leave pages, and potentially the quantity of snaps. These are not connected to any data that is actually recognizable. The motivation behind the data is for investigating patterns, regulating the webpage, following clients’ development on the site, and assembling segment data.
Treats and Web Guides
Like some other site, Ehsaas Program utilizes “treats”. These treats are utilized to store data including guests’ inclinations, and the pages on the site that the guest got to or visited. The data is utilized to streamline the clients’ insight by tweaking our website page content in light of guests’ program type or potentially other data.
Google DoubleClick DART Treat
Google is one of an outsider seller on our site. It likewise utilizes treats, known as DART treats, to serve advertisements to our webpage guests in view of their visit to www.website.com and different locales on the web. Notwithstanding, guests might decide to decline the utilization of DART treats by visiting the Google promotion and content organization Security Strategy at the accompanying URL – https://policies.google.com/advancements/advertisements
Publicizing Accomplices Protection Arrangements
You might counsel this rundown to find the Protection Strategy for every one of the publicizing accomplices of Ehsaas Program.
Outsider promotion waiters or advertisement networks utilizes advancements like treats, JavaScript, or Web Reference points that are utilized in their particular notices and connections that show up on Ehsaas Program, which are sent straightforwardly to clients’ program. They consequently accept your IP address when this happens. These advancements are utilized to quantify the viability of their publicizing efforts or potentially to customize the promoting content that you see on sites that you visit.
Note that Ahsas Program has no admittance to or command over these treats that are utilized by outsider promoters.
Outsider Protection Strategies
Ahsas Program’s Protection Strategy doesn’t matter to different publicists or sites. Consequently, we are encouraging you to counsel the particular Protection Strategies of these outsider promotion servers for more definite data. It might incorporate their practices and guidelines about how to quit specific choices. You can decide to impair treats through your singular program choices. To know more definite data about treat the executives with explicit internet browsers, it very well may be found at the programs’ individual sites.
CCPA Security Freedoms (Don’t Sell My Own Data)
Under the CCPA, among different freedoms, California shoppers reserve the option to:
Demand that a business that gathers a buyer’s very own information unveil the classifications and explicit bits of individual information that a business has gathered about shoppers.
Demand that a business erase any private information about the purchaser that a business has gathered.
Demand that a business that sells a purchaser’s very own information, not sell the customer’s very own information.
In the event that you make a solicitation, we have one month to answer you. In the event that you might want to practice any of these privileges, kindly reach us.
GDPR Information Security Privileges
We might want to ensure you are completely mindful of every one of your information assurance privileges. Each client is qualified for the accompanying:
The option to get to – You reserve the privilege to demand duplicates of your own information. We might charge you a little expense for this help.
The right to amendment – You reserve the option to demand that we right any data you accept is incorrect. You additionally reserve the privilege to demand that we complete the data you accept is deficient.
The right to deletion – You reserve the option to demand that we eradicate your own information, under specific circumstances.
The option to limit handling – You reserve the privilege to demand that we confine the handling of your own information, under specific circumstances.
The option to protest handling – You reserve the privilege to have a problem with our handling of your own information, under specific circumstances.
The right to information convenientce – You reserve the option to demand that we move the information that we have gathered to another association, or straightforwardly to you, under specific circumstances.
In the event that you make a solicitation, we have one month to answer you. Assuming you might want to practice any of these freedoms, kindly reach us.
Kids’ Data
One more piece of our need is adding security for youngsters while utilizing the web. We urge guardians and gatekeepers to notice, partake in, or potentially screen and guide their internet based action. Ahsas Program purposely gathers no Private Recognizable Data from youngsters younger than 13. Assuming you believe that your kid gave this sort of data on our site, we unequivocally urge you to reach us right away and we will do our earnest attempts to eliminate such data from our records quickly.
Changes to This Security Strategy
We might refresh our Protection Strategy every once in a while. Accordingly, we encourage you to survey this page intermittently for any changes. We will inform you of any progressions by posting the new Security Strategy on this page. These progressions are taking effect right now, after they are posted on this page.